Articles
e-SHRAM Portal for Registration of Unorganized Labourers of India
e-SHRAM is the first ever national database of unorganized workers. It aims at registering 38 Crore unorganized labourers engaged in construction, migrant workers, gig and platform workers, street vendors, domestic and agriculture workers, milkmen, fishermen, truck drivers, etc.
Faridkot District, Punjab Transforming the Rural District into Advance Digital One
Since its inception in late 80, the District Unit is a pioneer in designing, developing and implementing many e-Governance Projects with an objective to use electronic means to support and stimulate good governance. NIC Faridkot is instrumental in rolling out the ICT awareness in the...
Tamil Nadu State - A Pioneer in Digital Governance
NIC Tamil Nadu State Centre provides consistent support to the Government of Tamil Nadu, Central Departments and PSU situated in Tamil Nadu, in their endeavours to fully develop e-governance solutions, specifically citizen centric solutions, for the benefit of the common man, and...
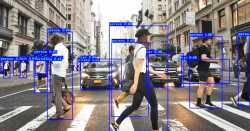
Object Detection Technologies - A simplified explanation of YOLO class of algorithms
It is of the highest importance in the art of detection to be able to recognise out of a number of facts which are incidental and which are vital
WEB APPLICATION FIREWALL -Defense against Layer-7 Attacks
The application layer (L7) is the hardest to defend. Hackers get direct access to the bounty they are seeking, by compromising layer-7. The need is to have a product with an understanding of the real-world techniques or methods hackers use. It is here that the Web Application Firewall...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


