Articles
Kerala State Delivering E-governance to the Door Step
NIC Kerala is playing a pivotal role in bringing IT close to the citizens with its ICT initiatives. Had a significant role in empowering the State Govt during the COVID pandemic with the IT enabled services provided in mission mode. NIC has taken a remarkable advancement in mobile application...
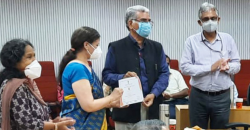
NIC TAG Awards and Launch Ceremony
NIC TAG group organised State Mobile App and WebApp UI/UX Contests in July 2021. The awards for these contests were presented by the Director-General, NIC Dr. Neeta Verma on 12th October 2021.
Blockchain Technology Driving the Next Generation eGovernance Applications
Blockchain technology has drawn significant attention from the Government due to the pain areas that it promises to address. Several schemes of the Government require the verification of the documents / facts to ensure the eligibility of the applicant. This is a time consuming process. Although...
Government Email Service Enabling secure communication channel within the Government
The importance of Email Service was evident during the ongoing pandemic as it ensured that communication within the Government is not impacted by COVID-19 and continues to operate seamlessly. The service is the largest service of its kind ffered by any Government globally.
PBOX Proctoring Based Online Examination System
PBOX provides the ability to conduct exam in a much scalable, secured and network resilient way with additional provision to be deployed in on-campus mode. It provides mechanism to do auto proctoring powered by AI /ML on the edge device itself without sending each frames to the server. It allows the...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (5.0 MB)
PDF (5.0 MB)

