Articles
Pithoragarh- Taking ICT to the Grassroots
Pithoragarh, the picturesque district of Kumaon region in Uttarakhand, with a breathtaking panoramic view of Himalayas, summons tourists worldwide to its alluring grandeur of natural beauty. Sharing borders with China (Tibet) on northern side and Nepal on the east, the district has a population of about...
West Singhbhum - Winner in Implementing ICT Projects
Adorned by hills and plateaus, spreading natural splendor with sparkling rivers amidst dense forests, harboring variety of flora and fauna, West Singhbhum, situated in the southern part of Jharkhand state. The largest district of the state, came into being in 1990, when the erstwhile Singhbhum district...
Purnea District: Cementing ICT for Masses
Constituted in the year 1813 the Purnea District comprises the eastern most part of the alluvial North Bihar plain. The name district was derived from the lotus flower, which was found in abundance in the past in the canal of Kosi and Mahananda rivers. Situated along the border of West Bengal &...
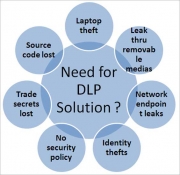
Data Leakage and Prevention Solution- The Next big thing in Security
Data Loss Prevention is one of the most hyped, and least understood, tools in the security space. In spite of the availability of many technologies, it can be difficult to understand the ultimate value of the tools and products best suited to the given problem. This report will provide the necessary...
Network Access Control and End Point Compliance
Cybercrime continues to rise, with the primary aim to compromise an organisations information that will make a profit for the perpetrators. To avoid the unwelcome publicity provoked by IT failures, securing the network is more important today than ever before. It's also tougher to achieve, as today's...




 Subscribe
Subscribe

 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


