Articles
Educating & Empowering Masses through IT
In an exclusive interview session with Informatics, Sh. Chandra Prakash, IAS Principal Secretary, IT & Electronics, GoUP talks about how the implementation of e-Governance initiatives is fast changing the image of Uttar Pradesh from an IT laggard state to an IT happening state.
CHHATTISGARH CHERISHING THE CHALLENGES
Thirty-six Forts once existed in the region are the basis of the name Chhattisgarh signifying it as The land of thirty six forts. It is also nick-named the rice bowl of India due to abundance and variety of rice produced here. The state is also blessed with wide range of natural resources like dense...
Tamilnadu- The Emerging Centre of e-Governance In India
The NIC State Unit of Tamilnadu is not only fostering impeccable ICT activities within the state but also has contributed substantially to growth in the Indian as well as the global ICT industry. With a large pool of highly skilled manpower and a solid backbone of old/new economy Infrastructure, Tamil...
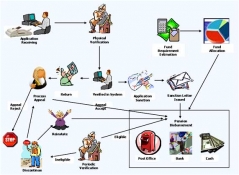
MIS for Indira Gandhi National Old Age Pension Scheme
Indira Gandhi National Old Age Pension Scheme is introduced by the Ministry of Rural Development, Govt. of India to provide a steady monetary assistance for all man and women of India above the age of 65 years of age and below poverty line. In addition to the existing IGNOAPS scheme, the Govt. Of India...
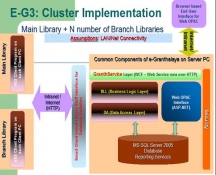
e-Granthalaya: A Digital Agenda for Library Automation and Networking
Libraries are the social institutions as they provide various kinds of services to the users and citizen of the city / country. They have been the essential part of the education system in the society since early days. In the modern India, libraries have become the integral part of not only educational...




 Subscribe
Subscribe

 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


