News
NIC Jhalawar Wins CSI Nihilent District Award
The seamless and valuable efforts of District Jhalawar (Rajasthan) in bringing good governance through utilization of ICT (Information and Communication Technologies) were appreciated at ceremony held on Dec. 2nd, 2012 as part of Annual Convention of Computer Society...
Haryana: Dynamic Integration of Property Registration, Land Records & Cadastral Maps Project Received CSI - Nihilent e-Governance Award 2011-12
The Haryana’s project Dynamic Integration of Property Registration, Land Records & Cadastral Maps has received CSI-Nihilent Awards 2011-12, under Projects Category, on December 02, 2012 at Science City Kolkata. The award was presented at the 47th Annual Convention of Computer Society of...
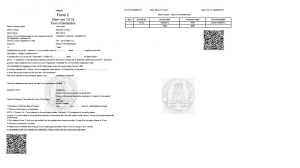
Launch of Online Issue of C and F Forms for Commercial Taxes Department, Tamilnadu
Objectives The system facilitates the authorized dealers to file online application and generation of C and F form by logging into the Web Site of Department of Commercial Taxes, Tamil Nadu. C and F Forms are generated based on the Monthly Returns filed with Annexures by the Dealers. For this...
NIC Mizoram got eNorth East Award on Query and Alert Based SMS Service
Query and Alert Based SMS service For Mizoram Transport Department” has been recognized by the Grand Jury as an award winner for eNorth East award 2012 under the category of “eGovernance and Public Service Delivery.” This prestigious award was presented by Hon'ble Minister,...
Online Question Answering Systems Inaugurated at Jharkhand State Assembly, Ranchi
The grand celebration organized on the twelfth anniversary of Jharkhand State Assembly got off with the inauguration of the online “Question – Answering System” of NIC at the newly established computer centre especially dedicated for purpose, by Dr. Syed Ahmad, Hon’ble Governor...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


