Health
OxyCare Monitoring Supply and Operation of Oxygen Devices in India
The timely availability of oxygen in Hospitals became a major requirement during the second wave of the COVID-19 pandemic in May June 2021. The Ministry of Health & Family Welfare, Government of India initiated the OxyCare project to ensure timely supply of various Oxygen equipment, installation...
Chikkaballapur Karnataka Ability to keep abreast of eGovernannce and its potential societal impacts
The IT revolution in Chikkaballapur started by NIC with the development of various in-house software apps as per the requirements of the District Administration and providing handson training and technical support to the stakeholders with full efficiency. This enabled transparency in the service delivery....
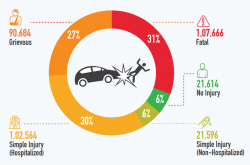
iRAD Making Better and Safer Road Ecosystems
iRAD Road Accidents have become a menace in India. iRAD tries to solve it by creating an integrated road accident database to help authorities to take proactive decisions and make Better and Safe Roads for All.
e-Hospital Suite Augmenting the Public Healthcare System Digitally
NIC has developed the e-Hospital suite with a vision to improve the delivery of healthcare services to the citizens across the country under the Ayushman Bharat Digital Mission. It is a one-stop solution which helps in connecting patients, hospitals and doctors on a single digital platform. Built on...
IVANI AI enabled Image & Video Analytics by NIC for effective & efficient eGovernance
Computer Vision is a field of Artificial Intelligence (AI) that enables computers and systems to derive meaningful information from digital images, videos and other visual inputs with help of Deep Learning Networks in Ideal Conditions. Some of the major applications of image analytics are object detection,...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


