Health
Malnutrition Monitoring System - Fostering the Implementation of ICDS in Malda, West Bengal
The system helps to sort the data based on different key parameters like child growth, MUAC (Mean Upper Arm Circumference) and breastfeeding status, and therefore to identify areas of concern and implement directed intervention. This system has recently upgraded to incorporate detailed information regarding...
Mid Day Meal Automated Reporting & Management System (MDM ARMS)
The Mid Day Meal Scheme is one of the most well-known schemes initiated by the Government of India. NIC, Himachal Pradesh has taken the initiative to push the effciency of the scheme to the next level using ICT by creating the MDM-ARMS software and a related mobile based App to improve the management...
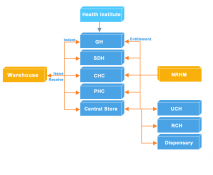
ONLINE DRUG INVENTORY & SUPPLY CHAIN MANAGEMENT SYSTEM OF HARYANA
With the aim to provide Right Quantity of Right Product on Right Place on Right Time in Right Condition at Right Cost for Right People and also to streamline the distribution of drugs to institutions and ensure availability of drugs at all times, a new, innovative system called online Drug Inventory...
e-Hospital@NIC: Simplifying Health Care Delivery
Tucked away at the southernmost tip of the Northeast, the state of Tripura has made significant contribution to public health care by pioneering e-Hospital@NIC-an integrated Hospital Management Information System (HMIS) which now runs in almost 30 major public hospitals across the country,...
CollabDDS: Network Enabled Medical Diagnosis and Education in Skeletal Imaging using X-Rays Dr. O. P. KHARBANDA
National Knowledge Network (NKN) due to high bandwidth and low latency has ensured the creation of applications which will be beneficial to all stakeholders in science, technology, governance and research & development. A model project funded by NKN and executed by NIC, New Delhi; AIIMS...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


