Health
Digital Village Harisal - Striding with the Digital Way of Tribal Development
Technology enablement activities took a big leap at Harisal village from March 2016. Since then, several organizations have partnered in initiatives to address gaps in the progressive path. Many more joined the path of transformation from mere digital technologies to smart technologies....
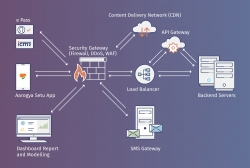
Aarogya Setu App
Aarogya Setu is a mobile application launched by the Government of India on 2nd April 2020, to aid the COVID-19 containment efforts of the Government. The App works based on contact tracing method and helps in identifying, monitoring and mitigating the spread of COVID-19 across the country
RT-PCR App - Mobile Application for Containment and Monitoring Covid-19 pandemic across the Country.
Covid-19 pandemic in India is part of the worldwide situation of coronavirus disease and a large number of people is likely to be affected by the coronavirus. The country has imposed initial lock-downs, supplemented by increased testing of people and contact tracing of patients as effective measures...
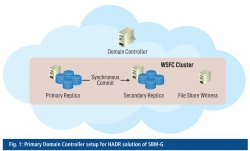
Swachh Bharat Mission - Gramin, Ensuring High Availability, Disaster Recovery and Design Implementation
The Swachh Bharat Mission -Gramin (SBM-G) programme, under the Ministry of Drinking Water and Sanitation, is a flagship programme of the Government of India. The e-Governance application used for its monitoring has been developed in-house by NIC under the guidance of the SBM-G programme division.
Fourth International Day of Yoga
The International Day of Yoga has been observed every year on 21st June since its inception in the year 2015. This year, The theme of the day was "Yoga for Peace". Encouraging health awareness among its officers and employees, the National Informatics Centre, in coordination with the Ministry...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


