Land Records
Bhagalpur : e-Governance in the Silk City of Bihar
Bhagalpur, situated on the southern banks of the holy River Ganga, is famous for producing Tassar silk and sarees and hence also known as the Silk city of Bihar. The important places to visit are the ancient Buddhist University at Vikramshila, Jain Temple at Nathnagar, Sahjangi and the Ajagaibinatha...
BHIWANI: Leveraging e-Governance Culture through ICT
Bhiwani city, named after a Rajput King wife Bhani, is also mentioned in Ain-e- Akbari. Bhiwani has been a prominent center of commerce since the time of the Mughals. District Bhiwani came into existence on 22nd December 1972. The district is spread over an area of 5099 Sq. Kms. and comprises of...
DHARANI:Digitally Signed Land Records of Goa
Even in the 21st century India, social status is very much defined by the piece of land one owns. Therefore, it is the obligation on the governments to have an efficient as well as an analytical mechanism to ascertain the ownership, type, and nature as well as cultivation pattern of the land. Manual...
Leveraging Emerging Technologies in Integrated Property Registration & Land Records SolutionIICT
Use of technology in registration of land records
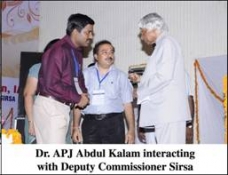
SIRSA: Revolutionizing Governance Through ICT
Sirsa is said to be one of the oldest places of Northern India and its ancient name was Sairishaka, which finds its mention in Mahabharata, Panini's Ashatadhayayi and Divyavadan. It must have been a flourishing city in the 5th century B.C. as mentioned by Panini. Sirsa forms the extreme...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


