ICT in Districts
Haryana:- DIO Sirsa commended by State Minister of Labour & Employment during International Geeta Jayanti Mahotsav 2017 at Sirsa
International Geeta Jayanti Mahotsav 2017 was celebrated in Ch. Devi Lal University, Sirsa (Haryana) w.e.f. 28.11.2017 to 30.11.2017. Sh. Naib Singh Saini, State Minister of Labour & Employment Haryana, Dr. Vijay Kumar Kayat, Vice Chancellor CDLU and Dr. Munish Nagpal, Addl. Deputy Commissioner...
Technical Support by NIC Himachal Pradesh in the Conduct of Assembly Elections 2017
Assembly Elections in Himachal Pradesh are scheduled to be held on 9th November 2017. NIC Himachal Pradesh has been providing technical support in the smooth implementation of IT solutions covering various stages of the election process. The District Election Information System (DISE)...
District Level Training on ERONET held at Cuttack, Odisha
A district level training programme on ERONET for all the EROs / AEROs / Supervisors / Data Entry Operators of Cuttack district was held in the Conference Hall, Collectorate, Cuttack on 23rd October, 2017 in 03 batches. 204 numbers of participants from the following Offices have attended the training, ...
Honourable Union Minister, MeitY Inaugurates VLE Conference, Dharamshala
Sh. Ravi Shankar Prasad, Hon’ble Union Minister for Electronics and Information Technology, Law and Justice, GoI Inaugurated the Common Service Centre-Village Level Entrepreneur (CSC VLE) Conference at Dharamshala, Himachal Pradesh on 2nd October 2017. More than a thousand Village Level Entrepreneurs...
His Excellency, Governor, Himachal Pradesh Honours NIC HP Officers at Kullu
His Excellency Acharya Devrat, the Hon’ble Governor of Himachal Pradesh honoured five officers of NIC Himachal Pradesh on 30th September 2017 in the International Dasehra Festival at Kullu for their contribution in developing the Online Rohtang Pass Permits software which has been implemented...




 Subscribe
Subscribe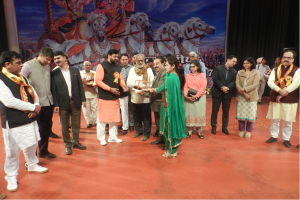





 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


