Technology
Service Oriented Architecture: In the Security Perspective
As electricity, if used tactfully then many useful things can be done but a little carelessness can make a big loss. As the same way Information, if accessed by the authorized person, produces effective output but unauthorized access to the same may create unpredictable nuisance. Many e-Governance...
Commercial Tax Computerisation in Uttar Pradesh
The introduction of Commercial Tax Computerisation in UP, has added a new dimension to the department, in dissemination of actual facts related to Commercial taxes at the service of the citizens. It will help the tax department, to effectively monitor the intrastate trade. Traders in Uttar Pradesh will...
Rainfall Monitoring System: Counting Rain Drops
Rainfall data plays important indicator role for monitoring crop situation in a drought / Flood year. Prediction of a drought like situation and early warning required to be issued to farmers / public as early as possible to face a natural calamity. Analysis of rainfall is also required for long term...
CPIS - Reforming Administration in Manipur
National Informatics Centre (NIC), Manipur State Centre was assigned to develop a computerized application for management of govt. employees, which would help state administration overcome the difficulties stated above. NIC Manipur designed & developed CPIS (Computerisation of Personnel Information...
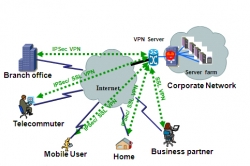
SSL VPN: A Technology Overview
In the world of distributed computing, corporate applications are hosted in data centers located in multiple locations and are accessed by many users from various locations. To provide secure access to such network resources, technocrats have designed Secure Socket Layer Virtual Private Network (SSL...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


