Technology
Hands free Computing by Integrating Speech Recognisation
Voice reorganization and text to speech system is becoming a powerful tool to provide the services through ICT for the physically handicapped people. While entering to ATM counters and just after swapping the ATM card in the reader, a greeting voice as well as guiding instruction can be heard in almost...
Software Engineering: An instrument for peace, progress and co-existence
Software engineering is a discipline for software developers and managers. They do practice to deliver software or product following guidelines by applying engineering techniques within process frameworks. The intentions is to enable people consume quality products or quality services. This creates positive...
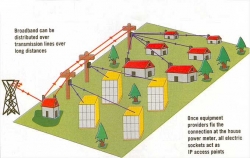
Broadband Over Powerlines: A Paradigm Shift
An emerging technology may be the newest heavy hitter in the competitive world of broadband Internet service. It offers high-speed access to your home through the most unlikely path: a common electrical outlet. With broadband over power lines, or BPL, you can plug your computer into any electrical outlet...
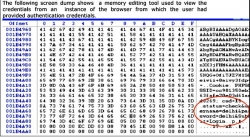
Salted Hashing of Passwords
During the course of Penetration testing of Web Applications at Cyber Security Division, NIC, several security vulnerabilities are identified. One of these vulnerabilities includes the finding that the credentials traveling in clear text can be sniffed from the network. The credentials can also be detected...
Guidelines for Indian Government Websites
Web enablement of citizen services is one of the focus areas of NeGP (National e-Governance Plan). Communication and literacy expression are the key indicators of a successful relationship and websites are the first point of interface in building these relationships. They also facilitate an efficient...




 Subscribe
Subscribe

 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


