Technology
Digital Library
Meaning of a Digital Library is different for different people, organizations and communities. For a school student a Digital Library is collection of digital documents, database, video games and leaning materials accessible via computer network. For a space scientist collection may be available over...
West Kameng: Building Confidence towards ICT Enabled Services
Located in a mountainous tract with altitude varying from 650 ft to 13714 ft - West Kameng District of Arunachal Pradesh derives its name from the Kameng river, a tributary of the mighty Brahmaputra that flows through the District. The district comprises five major tribes: Monpa (which makes up 78% of...
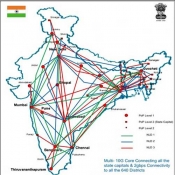
National Knowledge Network
It is beyond doubts that creation of National Knowledge Network (NKN) is an absolute necessity for the development of the nation. NKN will enable scientists, researchers and students from different backgrounds and diverse geographies to work closely for advancing human development in critical and emerging...
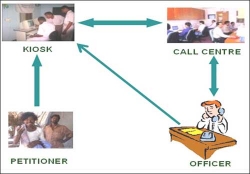
Prajavani- An e-Gov initiative for People voice through Local Language in Andhra Pradesh
Prajavani is an e-Governance initiative by the combined efforts of District Administration and National Informatics Centre in Ranga Reddy District (AP, India). The initiative is not only giving a practical shape to the Right to Information Act, but it is also creating job opportunities for the educated...
Screen Readers and designing Accesible Websites
It is responsibility of every website developer to ensure designing "Barrier Free" websites to ensure that people with disabilities have equal to the website.




 Subscribe
Subscribe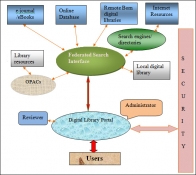


 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


