Technology
Harsamadhan: Building Citizen Confidence through Transparency
The prime focus of government is timely and effective redressal of public grievances, which leads to citizen satisfaction and credibility of government in Public Delivery systems. With this in mind, the Department of Administrative Reforms & Public Grievances, Government of India in technical...
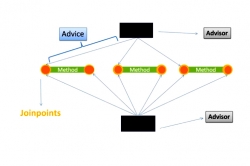
Aspect Oriented Programming
There are already a lot of robust programming methodologies like "Object Oriented Programming", "Procedural Programming" and "Distributed OOP". So, is it really a necessity to have another programming methodology named "Aspect Oriented Programming"? Is "Aspect...
Promise of HTML5
The Hypertext Markup Language (HTML) is meant for describing the structure of the Web Pages. HTML5 is the newest major revision of HTML. It has been built around the principles of Compatibility, Utility, Interoperability and Universal Access. Its goal is to improve semantics, efficiency, and...
Efficient Centralised Software using Office Business Applications
Centralized Software are the genre of applications which uses the latest advancements in technology providing solutions that are easier to implement, saves in a lot of money and are highly scalable. Implementing Centralized Software using Office Business Application results in effective harnessing...
Smart Card Based Projects in Government
Computer chip-embedded plastic cards that store and transact data, Smart cards, a new form of fast and effective transaction has been instrumental in providing better egovernance in India. Smart cards usually have multipurpose lives, from being National ID cards to tools for driving licenses...




 Subscribe
Subscribe


 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


