Technology
Self Healing Software System to Fix Post Release Errors
Availability & Reliability are the two critical terms used basically to describe the robustness of any software system but these two parameters are affected mostly by post released errors. The biggest loophole in current system is the lack of adequate intelligence in the software to response reactively...
Imphal East: e-Governance Deep Rooted with Land Records & CICs
With the computerization of "Land Records" i.e. Loucha Pathap, covering sixty five villages, and the establishment of Community Information Centres (CICs), the district stands apart from others. The computerization effort by the district administration in association with NIC in...
OCMMS for State Pollution Control Board
Online Consent Management & Monitoring System for State Pollution Control Board (OCMMS) is web based Generic Model for implementing a well-coordinated system applicable to most SPCBs and PCCs. This system allows industries for the online submission of application for CTE/CTO & for various categories...
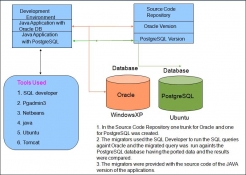
Migrating Applications to PostgreSQL - Experiences
Open Technology Centre (OTC) had undertaken migration of few legacy applications to Open Source Based Application. The migration has to be applied at multiple layers depending up on the design principle used by the application. The article shares the migration process utilized, the issues that are...
The National Knowledge Network: Making the Knowledge flow
When the Cabinet Committee on Infrastructure (CCI) entrusted the country nodal ICT organization, the National Informatics Centre (NIC), with the responsibility of establishing the Rs 5,990-crore National Knowledge Network (NKN) on March 25, 2010, it signaled the evolution of Indian ICT from an information-based...




 Subscribe
Subscribe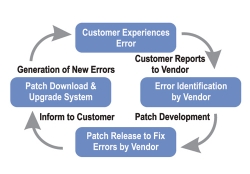


 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


