Technology
Multidimensional Data Modelling Concepts
Multidimensional data modelling is used for the designing Data warehouse, which will help in surround facts with as much relevant context dimensions. Multidimensionality is a design technique that separates the relational data into facts and dimensions. Multidimensional model present information to the...
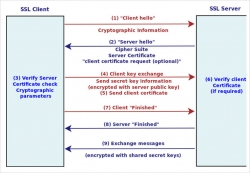
Secure Your Server Through SSL
In the recent times, we have been using the Internet for many of our online transactions such as Online Ticket reservation, online banking etc.We also observe that at times the data / information are being hacked without the knowledge of the user. However, technology can be used to minimize the risk...
User Rating for Web Resources
A Government portal is widely understood and viewed as a single window platform for the integrated delivery of information and services by the Government to its Citizens. Government portals are constituent of a huge content repository which is a culmination of information sourced from and...
Cufon: Custom Font Embedding Technique for Web
Cufon, pronounced as Koofo, is one among the popular font replacement techniques of its kind, which has attained much attention and popularity among web developers. Thanks to Simo Kinnuenen, a Finland-based web guru who developed this technique, which has evolved and enabled us to use non-web,...
Mobile e-Governance Services
Mobile e-Governance services is an integration technology. It best demonstrates its value when integrating heterogeneous systems because it supports many kinds of programming languages, run times, and networks. When there is a need to connect applications from incompatible environments, the...




 Subscribe
Subscribe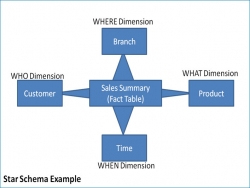




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


