Education
HTML Canvas & Fabric.js Open-source 2D Geometry Rendering JavaScript Library
Fabric.js is an open source 2D graphic library which can be used to give attractive visual effects,design games, interactive art, geometrical entities and calculation, etc.2D graphics has brought a revolution in web design by proving scenes and animations. CollabGEO -Collaborative 2D geometrical tool...
Sri Ganganagar, Rajasthan Creating Opportunities in the Agrarian District through ICT
In 1988, NIC Sri Ganganagar District Centre was established as a nodal ICT agency in the district. Since then, it has served as a platform to promote ICT initiatives, thus facilitating G2C and G2G services to the citizens. Through its website, the Centre is providing the citizens, information on...
Chikkaballapur Karnataka Ability to keep abreast of eGovernannce and its potential societal impacts
The IT revolution in Chikkaballapur started by NIC with the development of various in-house software apps as per the requirements of the District Administration and providing handson training and technical support to the stakeholders with full efficiency. This enabled transparency in the service delivery....
Blockchain Technology Driving the Next Generation eGovernance Applications
Blockchain technology has drawn significant attention from the Government due to the pain areas that it promises to address. Several schemes of the Government require the verification of the documents / facts to ensure the eligibility of the applicant. This is a time consuming process. Although...
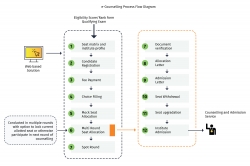
e-Counselling Services
e-Counselling services developed by NIC are the result of a focussed effort to put the best use of technology for bringing transparency in the admission process of the educational institutions in our country. This has also led to the implementation of a common selection process across...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


