Education
Comprehensive Web Content Management and Workflow System Efficient, Secure, and Dynamic Content & Workflow Management
This platform delivers an intuitive, feature-rich, and secure environment for managing websites and workflows. It incorporates tools for content editing, form management, and role-based publishing. Its innovative architecture enables dynamic form creation with validation and workflow-based form...
Mitigating Cybersecurity Misconfigurations Exploring Common Cybersecurity Misconfigurations and Effective Techniques for Securing Digital Infrast
Cybersecurity landscape is an ever-evolving battleground in this age of rapid digital transformation. Organizations must stay one step ahead of adversaries to protect digital infrastructures effectively. The National Security Agency and Cybersecurity and Infrastructure Security Agency have...
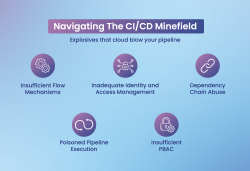
Securing CI/CD Pipelines Addressing the Unique Challenges in DevOps
CI/CD pipelines enable fast software delivery but come with security risks like weak flow control, IAM gaps, and dependency exploits. Mitigation includes role-based access control, multi-factor authentication, secure secrets management, and automated testing. Tools like Jenkins and GitLab CI/CD...
Online Policy-Based Transfers System A Comprehensive System for Implementation of Bulk Transfers
The Online Policy-Based Transfers System simplifies employee movement within the government, replacing paperwork with digital efficiency. It orchestrates seamless transfers across departments, streamlining processes and ensuring clarity and precision in each movement. Recognized for modernization, it...
Cyber Risk Insurance Insurance Policy to cover financial liabilities arising from cyber incidents
Cyber Risk Insurance, also simply known as Cyber Insurance, is a kind of insurance policy which protects business houses as well as individuals from financial losses due to cyber-related incidents. These incidents include various forms of cyber-crimes such as data breaches and cyber-attacks. The...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (5.0 MB)
PDF (5.0 MB)


