Education
Single Window Clearances System
The Government of Haryana, as an initiative to promote business in the State, has simplified the process through the Single Window Clearances System, which facilitates prospective investors to obtain regulatory clearances online through Haryana Enterprise Promotion Board under Empowered Executive Committee.
Chanakya: Registration & Examination System
CHANAKYA, the Registration and Examination System is a web enabled, role & workflow based software solution for the Universities and Educational Institutions to accomplish various tasks for enrolment, registration and examination.
Joint Seat Allocation System
Joint seat allocation to government funded technical institutes based on three independent entrance examinations using multiple ranks is a watershed event in engineering admissions in India.
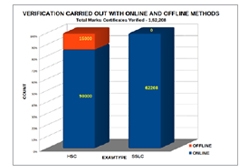
Mark Certificate Verification System for Directorate of Government Examinations, Tamil Nadu
The Directorate of Government Examinations conducts massive board examinations, for which they issue about Eight lakhs of Higher Secondary Course Certificates, Twelve lakhs of Secondary School Leaving Certificates and Fifty thousand Diplomas for Elementary Education every year. The National Informatics...
Pre-Examinations Monitoring System for Anna University, Chennai
Anna University, a unitary type of University, offers higher education in Engineering, Technology and Allied Sciences relevant to the current and projected needs of the society in Tamil Nadu. There are about 580 affiliated engineering colleges and these colleges offer various engineering degrees...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


