Trainings
Workshop on eSamikSha Online System conducted at Conference Room, Cabinet Secretariat, Rashtrapati Bhawan, New Delhi on 06th November 2014
“eSamiksha portal, a real time, on-line system for monitoring of follow-up action on the decisions taken during the presentations made by different Ministries/Departments to the Prime Minister on various subjects like Infrastructure Target, Improving Work Environment, ...
WORKSHOP ON STATE PROJECTS MANAGEMENT PORTAL CONDUCTED AT LUCKNOW, UTTAR PRADESH
“ePMS, an On-line Project Management System for Uttar Pradesh tracks the projects involving investment 100 crore to 1000 crore. It enhances the efficiency, bring transparency and improve the communication between industries to Government and State to Centre or vice versa. It automates the entire...
Workshop on State Projects Management Portal conducted at Mumbai on 25th and 26th September 2014
“ePMS, an On-line Project Management System for Maharashtra tracks the projects involving investment 100 crore to 1000 crore. It enhances the efficiency, bring transparency and improve the communication between industries to Government and State to Centre or vice versa. It automates the entire...
Two days training workshop on State Projects Management Portal conducted at Ranchi on 18th and 19th September 2014
“ePMS, an On-line Project Management System for Jharkhand tracks the projects involving investment 100 crore to 1000 crore. It enhances the efficiency, bring transparency and improve the communication between industries to Government and State to Centre or vice versa. It automates the entire...
Workshop on State Projects Management Portal conducted at Patna on 4th and 5th September 2014
“ePMS, an On-line Project Management System for Bihar tracks the projects involving investment 100 crore to 1000 crore. It enhances the efficiency, bring transparency and improve the communication between industries to Government and State to Centre or vice versa. It automates the entire tracking...




 Subscribe
Subscribe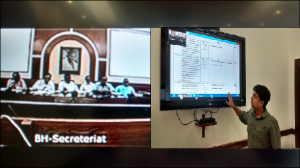





 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


