Cyber Governance
NIC is our Partner for e-governance Since the Creation of the State
Shri Jyoti Bhramar Tubid, a 1983 batch IAS officer of the state and posted as Principal Secretary, Department of Home, Govt. of Jharkhand. In an interview with us he reveals his views and plans about ICT specifically for the Department of Home & Police and in general about the present e-governance...
BALANGIR -IN QUEST OF EXCELLENCE
Balangir district, the cultural hub of Western Orissa, is spread over a total geographical area of 6569 sq. km. Comprising mostly of tribal inhabitants. Balangir district encompasses a population of 13,37,194 as per the census data of 2001 in 6 tehsils, 14 blocks and 1794 villages. The district bears...
Bundi: From Miniature Paintings to Excellence in ICT
Bundi named after a Meena Chieftain Bunda is called the queen of Hadoti region of Rajasthan. Thousands of tourists both domestic and foreign come here to see and discover this beautiful place. The finest variety of basmati rice is grown in the district and exported the world over. Bundi sandstone is...
West Bengal: Transforming With Widespread Adoption of ICT
West Bengal - a leading state in Eastern India, famous worldwide for Darjeeling Tea produced in the northern hill region and Royal Bengal tigers found in the Sunderbans on its southern part forming the worlds largest delta by the mighty rivers Ganges, Brahmaputra and Meghna.West Bengal can boast of...
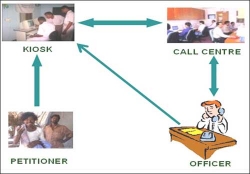
Prajavani- An e-Gov initiative for People voice through Local Language in Andhra Pradesh
Prajavani is an e-Governance initiative by the combined efforts of District Administration and National Informatics Centre in Ranga Reddy District (AP, India). The initiative is not only giving a practical shape to the Right to Information Act, but it is also creating job opportunities for the educated...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


