Networking
e-Office: COLLABORATION AND MESSAGING SERVICE
eOffice-CAMS is focused on providing effective communication between departmental applications through collaboration and the obvious solution is to have Collaborative service. The idea is to facilitate action oriented team to work together over a geographical distance and let internal users, systems...
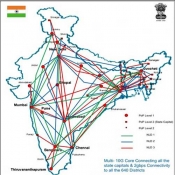
The National Knowledge Network: Making the Knowledge flow
When the Cabinet Committee on Infrastructure (CCI) entrusted the country nodal ICT organization, the National Informatics Centre (NIC), with the responsibility of establishing the Rs 5,990-crore National Knowledge Network (NKN) on March 25, 2010, it signaled the evolution of Indian ICT from an information-based...
National Knowledge Network
It is beyond doubts that creation of National Knowledge Network (NKN) is an absolute necessity for the development of the nation. NKN will enable scientists, researchers and students from different backgrounds and diverse geographies to work closely for advancing human development in critical and emerging...
Closed Circuit Surveillance System at Delhi Tihar Prisons
In major initiative to strengthen its security and surveillance on the activities of Prisoners in Delhi Tihar Prisons, the prison administration has geared up with the installation of Close Circuit Televisions (CCTV), covering major portions of the prison. With state of art CCTV control room being set...
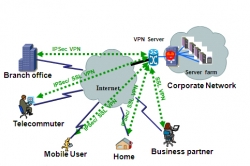
SSL VPN: A Technology Overview
In the world of distributed computing, corporate applications are hosted in data centers located in multiple locations and are accessed by many users from various locations. To provide secure access to such network resources, technocrats have designed Secure Socket Layer Virtual Private Network (SSL...




 Subscribe
Subscribe

 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


