Networking
e-CCI: PROJECTS MANAGEMENT SYSTEM
With an objective to create an institutional mechanism for tracking the stalled investment projects, both in the public and private sectors, and to eradicate the implementation bottlenecks so faced on a fast track basis, a Cabinet Committee on Investment (CCI) Cell has been constituted in the Cabinet...
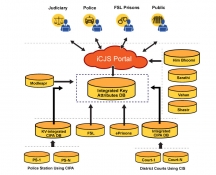
iCJS: Inter-operable Criminal Justice System
The Interoperable Criminal Justice System (iCJS) has been developed for the process of speedy justice by facilitating data-exchange between the courts, police/prosecution, jails and the forensic labs. The application has been developed by NIC for the District courts, prisons and Police...
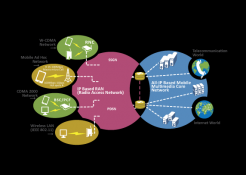
LONG TERM EVOLUTION(4G) - A Generation Gallop Technology
Earlier, downloading a large file used to take 30 minutes to a couple of hours depending on the broadband speed. Now the same task is possible in few minutes time even while on travel! The LTE (Long Term Evolution or 4G) has made this possible with its lightning fast Internet capabilities.
JABALPUR: Moving Towards Good Governance
National Informatics Centre, Jabalpur has been spearheading in promoting e-Governance culture in the district administration and other offices. NIC is providing multifaceted Information Communication Technology based initiatives for betterment of services delivery to the citizens living in...
ON-LINE WEB COUNSELING
State Council of Higher Education (APSCHE), Department of Technical Education (DTE) of Government of Andhra Pradesh and National Informatics Center (NIC),Govt. of India together evolved a new system for students' admission into various technical courses in various colleges across the state, through...




 Subscribe
Subscribe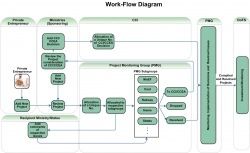



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


