Networking
Puducherry UT French Riviera of the East
NIC, Puducherry UT plays a vital role in designing, developing and implementing ICT solutions which has helped in achieving transparency and efficiency in the delivery of the citizen centric services. In addition to core infrastructure for networks, VC and cloud services, NIC Puducherry has established...
Bilaspur, Chhattisgarh Using ICT for Good Governance committed towards Digital Governance
Bilaspur is swiftly transitioning from an argarian district to a digitally enabled knowledge district. Its citizens are rapidly adopting digital products and services, which has propelled the district onto the Digital India map. In order to leverage this transition, the NIC Bilaspur District Centre is...
Bhagalpur : e-Governance in the Silk City of Bihar
Bhagalpur, situated on the southern banks of the holy River Ganga, is famous for producing Tassar silk and sarees and hence also known as the Silk city of Bihar. The important places to visit are the ancient Buddhist University at Vikramshila, Jain Temple at Nathnagar, Sahjangi and the Ajagaibinatha...
e-TOURISM: Streamlining Tourism Using ICT
Haryana is one of the most industrialized states in India. It is also known all over the world for its culture and religious & historical events like Mahabharta. Tourists and businessmen from all over the world visit this state. To expose the tourism potential of Haryana to the world,...
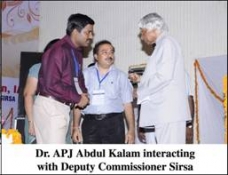
SIRSA: Revolutionizing Governance Through ICT
Sirsa is said to be one of the oldest places of Northern India and its ancient name was Sairishaka, which finds its mention in Mahabharata, Panini's Ashatadhayayi and Divyavadan. It must have been a flourishing city in the 5th century B.C. as mentioned by Panini. Sirsa forms the extreme...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


