e-Services
e-Shramik: Online Registration for Welfare of Odisha Building and Other Construction Workers
The Odisha Building and Other Construction Workers Welfare Board (OB&OCWW) was constituted to regulate the employment and service condition of building and other construction workers and to provide them safety, health and welfare measures. e-Shramik project aims to facilitate the construction workers...
Digital India Week (Launch on 01st July, 2015 at Indira Gandhi Indoor Stadium, New Delhi)
Digital India, a flagship programme of the Government of India, aims to transform India into a digitally empowered society and knowledge economy. This programme centres on three key vision areas of Infrastructure as a Utility to Every Citizen, Governance and Services on Demand and Digital Empowerment...
PEARL Suite: Property Registration for Government of Kerala
As part of e-governance, to carry out all the activities of Sub Registrar offices in Kerala, Windows based client-server application PEARL was initiated in the year 2000 and was implemented in all the 311 offices in Kerala. Even though the system automated the activities of SRO, the decentralized data...
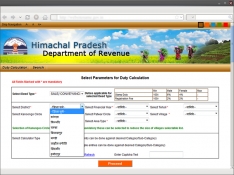
Himachal Integrated Registration Information System (HIMRIS)
Registration of deeds is the first and the most critical step in acquiring title to land or property and thus, assumes significance for those who are involved in these transactions. The registration of these transactions is mandatory to make them legal, otherwise ownership rights cannot be claimed/transferred....
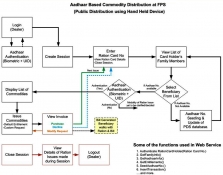
Implementation of Aadhar based Public Distribution System in Jharkhand
The Food, Civil Supplies & Consumer Affairs Department, Govt. of Jharkhand decided to develop Aadhar based, web enabled - Public Distribution System (PDS) using Hand held Terminals (HHT) at the 23614 Fair Price Shops (FPS) in the state. This enables end-to-end use of ICT ranging...




 Subscribe
Subscribe


 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


