G2C
Pithoragarh- Taking ICT to the Grassroots
Pithoragarh, the picturesque district of Kumaon region in Uttarakhand, with a breathtaking panoramic view of Himalayas, summons tourists worldwide to its alluring grandeur of natural beauty. Sharing borders with China (Tibet) on northern side and Nepal on the east, the district has a population of about...
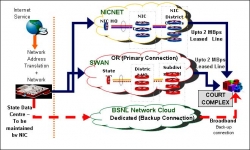
e-Courts Mission Mode Project: The Journey so Far
ICT enablement of judiciary is being pursued vigorously across the world. In India, ICT enablement of higher judiciary started in early nineties, covering the Supreme Court and all the 21 High Courts. Today, we have reached a stage where deployment of ICT in Supreme Court and the High Courts has reached...
Andhra Pradesh: A Right Place for Technology Breeding
Andhra Pradesh also known as the Rice Bowl of India is the fourth largest state in India. The state is not only famous for its rich culture and heritage but also a favourite place for tourists worldwide for its spellbound beaches. Of late the state has received lots of accolades in the global platform...
Right to Information Act - A Legal tool against India Cyber-divide
Mohammad Haleem Khan spoke exclusively to Informatics on Right To Information Act and CICs ICT initiatives to empower the citizen to avail information they so desired:
Rolling out NIC-GeP- the e-Procurement system in Orissa
Orissa has been the leading state in India to implement NIC-GeP -electronic procurement system by leveraging the Information Technology tools & the best practices. The success story in government sector has inspired the Corporations / Government undertakings like IDCO, IPICOL, Gridco, and OMC...




 Subscribe
Subscribe


 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


