G2C
Meghalaya - Using ICT to Metamorphose Governance
Meghalaya - Blessed with abundant rainfall, sunshine, virgin forests, high plateaus, tumbling waterfalls, crystal clear rivers, meandering streams - the state, carved from the erstwhile state of Assam - bounds it on the North and East while the South and West is covered by Bangladesh.
Educating & Empowering Masses through IT
In an exclusive interview session with Informatics, Sh. Chandra Prakash, IAS Principal Secretary, IT & Electronics, GoUP talks about how the implementation of e-Governance initiatives is fast changing the image of Uttar Pradesh from an IT laggard state to an IT happening state.
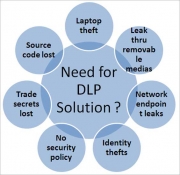
Data Leakage and Prevention Solution- The Next big thing in Security
Data Loss Prevention is one of the most hyped, and least understood, tools in the security space. In spite of the availability of many technologies, it can be difficult to understand the ultimate value of the tools and products best suited to the given problem. This report will provide the necessary...
West Singhbhum - Winner in Implementing ICT Projects
Adorned by hills and plateaus, spreading natural splendor with sparkling rivers amidst dense forests, harboring variety of flora and fauna, West Singhbhum, situated in the southern part of Jharkhand state. The largest district of the state, came into being in 1990, when the erstwhile Singhbhum district...
CHHATTISGARH CHERISHING THE CHALLENGES
Thirty-six Forts once existed in the region are the basis of the name Chhattisgarh signifying it as The land of thirty six forts. It is also nick-named the rice bowl of India due to abundance and variety of rice produced here. The state is also blessed with wide range of natural resources like dense...




 Subscribe
Subscribe


 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


