G2C
Bundi: From Miniature Paintings to Excellence in ICT
Bundi named after a Meena Chieftain Bunda is called the queen of Hadoti region of Rajasthan. Thousands of tourists both domestic and foreign come here to see and discover this beautiful place. The finest variety of basmati rice is grown in the district and exported the world over. Bundi sandstone is...
State in Focus Maharashtra: Connecting People and Government
The word Maharashtra, the land of the Marathi speaking people, appears to be derived from Maharashtri, an old form of Prakrit. Located in the north centre of Peninsular India, with a command of the Arabian Sea through its port of Mumbai, Maharashtra has a remarkable physical homogeneity, enforced by...
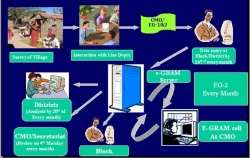
e-Gram in Rajasthan: An ICT Initiative to Transform Rural Governance
Information plays a very crucial role in overall development of the society, and easily accessible information results in a healthy and dynamic democracy. The growing innovations in the use of Information and Communication Technologies have opened up new era of information dissemination. This becomes...
West Bengal: Transforming With Widespread Adoption of ICT
West Bengal - a leading state in Eastern India, famous worldwide for Darjeeling Tea produced in the northern hill region and Royal Bengal tigers found in the Sunderbans on its southern part forming the worlds largest delta by the mighty rivers Ganges, Brahmaputra and Meghna.West Bengal can boast of...
Kanpur Dehat: Serving Rural Citizens at their Doorstep
ICT is fast spreading by virtues of its adoption in various sectors serving the citizens. NIC, Kanpur Dehat, established in 1988, has been serving the rural masses by facilitating the district administration, development departments and citizens through small and large IT based initiatives.




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


