Articles
E-Dashboard for Elections
e-Dashboard is a web based online application which was launched by Haryana during the 5th general election for Municipalities of ULBs. Developed and successfully implemented by NIC Haryana, this application enhances transparency in the entire election process and has evolved to be used as an integral...
HOT DAK Tracking System
HOT DAK Tracking System was conceived and developed for online tracking of important and High Priority References across the Offices to monitor and achieve timely disbursal of References.
e-Seed - The One Stop, Non-Stop Aadhaar- Enabled Seed Distribution System
e-Seed fetches land holdings information of each farmer from webland database, based on his/her Aadhaar number to decide seed eligibility.
oAuth Based Single Sign-On
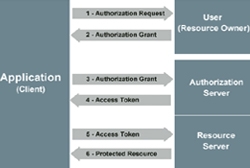
Introduction of oAuth 2.0 based Single Sign-On authentication mechanism in MyGov has enabled better user experience while accessing its various sites and Apps.
HP Telestroke Mobile App
The HP Telestroke, Android based Mobile App, developed for the citizens, 108 Ambulance personnel and Doctors is proving a boon to the Stroke patients in the State saving lives and educating the masses about the action to be taken in case of such a stroke.




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


