Articles
DND Services App of TRAI
Subscribers can activate the Do Not Disturb (DND) Services by TRAI by using this App. By activating the DND services, the telecom provider can block/ take action against the numbers from which consumers are getting such calls or messages.
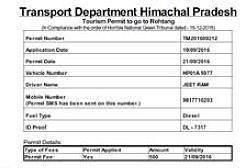
Online Rohtang Pass Permits Issuance System
To make it easier for the Rohtang Pass commuters, the payment gateway has been integrated with the system so that all the charges can be paid online and the permit is issued on successful receipt of payment by the Department. This web application is a unique mode of getting permits.
Indian Customs EDI Systems (ICES)
The Indian Customs EDI Systems (ICES) automates more than 98% of India's Imports and Exports and is a major catalyst in speedy and transparent Customs clearances at Air Cargoes, Sea Ports and Inland Custom Stations. The dynamics of the trade have been diligently incorporated in the form of software...
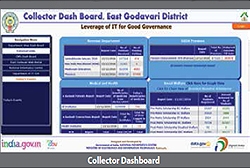
East Godavari, Andhra Pradesh
East Godavari NIC Centre provides ICT based solutions to the District Administration and various Central, State and Quasi Government offices located in the district. It is the first district in the Country to utilize Aadhaar based biometric authentication services for Government To Citzens (G2C) Applications.
Gurugram, Haryana
Several ICT based activities have taken place in Gurugram for better eGovernance. The District has pioneered many innovative initiatives such as GIS interventions, usage of Unmanned Aerial Vehicle (UAV) for Land Records Management, Urban Planning etc. which have raised the benchmark for District Informatics...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


