Articles
The National Meet on Grassroot Informatics
India has been making progress in the field of Information and Communication Technology with leaps and bounds. This progress, however, would not have been possible without the contributions of the officers closest to the ground reality, the District Informatics Officers (DIO).
Union Minister Inaugurates Digital Government Research Centre (DGRC) in Patna
DGRC is a centre of excellence which strives to nurture, visualize and implement ideas in the field of eGovernance research and innovation
Bihar State ICT Initiatives:Soaring High With Excellence In m-Governance
NIC Bihar has been identified as a Mobile Competency Centre and has been involved with the design and development of several key Apps for various departments at a variety of levels of administration.
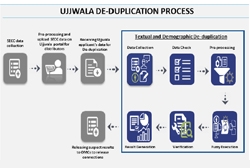
Ujjwala-Textual and Demographic De-duplication
India is widely touted as an emerging economic power, but nearly half of the country still cooks with firewood. According to 2011 census, only 28.5% of the 1.3 billion population across India uses LPG/ PNG for cooking. Pradhan Mantri Ujjwala Yojana (PMUY) aims at providing 5 crore free LPG connections...
Samrakshane: Portal for Crop Insurance
According to World Bank, approximately 60 percent of India's land area is used for agricultural purpose making India second largest in terms of agricultural land availability. Major chunk of this agricultural land is rain-fed (60% of total agricultural land) and India ranks first among the rain-fed...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


