Articles
HARIDWAR: Demystifying Haridwar with use of ICT
Haridwar, the paradise for nature lovers, presents a kaleidoscope of Indian culture and civilization. The word Haridwar or Hari-ka-dwar literally means Gateway to God. River Ganga, one of the major rivers of northern India, worshipped as a Goddess, runs through the district making Haridwar...
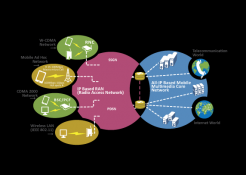
LONG TERM EVOLUTION(4G) - A Generation Gallop Technology
Earlier, downloading a large file used to take 30 minutes to a couple of hours depending on the broadband speed. Now the same task is possible in few minutes time even while on travel! The LTE (Long Term Evolution or 4G) has made this possible with its lightning fast Internet capabilities.
HIMACHAL PRADESH- Setting New Paradigms in ICT
Proclaimed by ancient Indian texts as Devbhumi - Land of the Gods- the beautiful, far-flung Himachal Pradesh has an almost palpable presence of divinity and is famous for its abundant natural beauty. Himachal Pradesh has a rich culture which is very much apparent in the day to day lives...
TAMIL NADU: The Success Story of a Premier IT Hub
The state of Tamil Nadu with its capital at Chennai has established itself as a leader in the IT industry with reliable and efficient infrastructure, excellent trained manpower skills, proactive approach of the state administration and a zeal to grow.
AUTOMATION OF COMMERCIAL TAX DEPARTMENT, UTTARAKHAND
The Commercial Tax Department of Uttarakhand is one of the major contributors to the state revenue. It mainly interfaces with business community and is responsible for administering value added tax (VAT), central sales tax (CST), and State Tax on entry of goods into the local market. Its functioning...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


