Articles
Commercial Tax Computerisation in Uttar Pradesh
The introduction of Commercial Tax Computerisation in UP, has added a new dimension to the department, in dissemination of actual facts related to Commercial taxes at the service of the citizens. It will help the tax department, to effectively monitor the intrastate trade. Traders in Uttar Pradesh will...
Digital Archiving and Management at National Informatics Centre
Digital objects are being created by governments, private corporations, authors, publishers, librarians, museum curators etc. in the form of text documents, photographs, images, audio and video footage, maps and more. Specifically, the massive volumes of paper generated by government offices can be pulled...
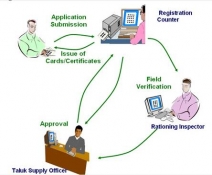
ICT an enabler for an efficient Public Distribution System in Kerala
Public Distribution of Food grains has always been an integral part of any State overall food policy. It has been evolved to reach the urban as well as the rural population in order to protect the consumers from the fluctuating and escalating price syndrome. TETRAPDS (Targeted Efficient Transparent Rationing...
Closed Circuit Surveillance System at Delhi Tihar Prisons
In major initiative to strengthen its security and surveillance on the activities of Prisoners in Delhi Tihar Prisons, the prison administration has geared up with the installation of Close Circuit Televisions (CCTV), covering major portions of the prison. With state of art CCTV control room being set...
Leveraging Web 2.0 in Government
A new genre of Web-based applications has gained a lot of popularity in last few years. Applications such as Facebook, YouTube, MySpace, Twitter, once a tool of tech savvy youngsters have gained a lot of popularity and acceptance across much wider spread of demography. Social-networking Web sites,...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


