Articles
ISES- Integrated Socio-Economic Survey of Students
The Government of Andhra Pradesh has desired to deliver the citizen-centric services from a centralized location through all citizen service centres such as e- Seva, AP Online, CSCs across the state under a new initiative called MeeSeva. A web based application- ISES has been designed and developed...
eOffice Knowledge Management System
eOffice KMS is a simple, easy to use and rich feature, browser based document management system. It transforms both paper and electronic documents into knowledge assets that can be instantly used by the organization workforce.
eDMAIs-Delivering Mechanized Agricultural Implements System
Improved farm implements and machinery are used for different farm operations to increase productivity of land and labour through timeliness of operations, efficient use of inputs, improvement in the quality of produce, safety and comfort of farmers, reduction in loss of produce and drudgery...
NIKSHAY- A web based solution for monitoring of TB patients
To monitor Revised National Tuberculosis Programme (RNTCP) effectively, a web-enabled and case-based monitoring application called NIKSHAY has been developed by National Informatics Centre (NIC). This is used by health functionaries at various levels across the country in association with...
Tribute to a Great Visionary: Dr. N. Seshagiri
Dr. N. Seshagiri, founder and the former Director General of National Informatics Centre, left for heavenly abode on Sunday the 26th of May 2013. Dr. Seshagiri was blessed with immense intellectual potential and high technical quotient. As the mastermind of the Nationwide Computer Network...




 Subscribe
Subscribe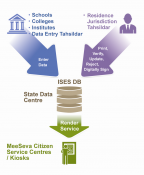





 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


