Articles
Enabling Effective Project Monitoring and Control in Government using web based CPM/Pert Technology
Enterprise Project management as a management discipline in Govt. underpins much economic activity. It is an effective project management that translates promises into well managed processes that improves everyday life. There is also an ever-increasing need and awareness to monitor closely the efficiency...
Office Suites - Best of Both Worlds
Innovations in technology have historically provoked profound changes in literacy acquisition and expression. From the development of the written alphabet to the printing press, changes in technology affect the way we think, write, and communicate and, by extension, the way we teach written communication....
Data Center Operations and Management
Data Centre management is a pretty complex task and needs a multidisciplinary, highly skilled team to effectively & efficiently manage it. Data Centre management requires additional IT attention and resources. The consequent write up is all about the management infrastructure involved in managing...
Publishing of Exam Results & Counseling from Internet Data-Centre NIC
Internet Data-Centre at NIC (HQ) has been hub for e-governance activities be it a website, portal or e-gov project in providing a robust, reliable and secure platform for service delivery. Among the thousands of web/portals/e-gov projects hosted by NIC Data Centre, Electronic Publishing of Exam results...
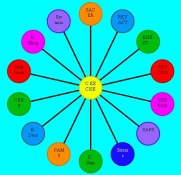
e-Governance In Central Excise And Service Tax
National Informatics Centre was entrusted the responsibility of computerisation of Central Excise Commissionerates, Central Board of Excise and Customs (CBEC), Ministry of Finance throughout the country in the year 1991. The first version was released in November 1991. Over the period, the SERMON...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


