Articles
Securing Your Desktop
In todays computing environment, the security of all computing resources, from network infrastructure devices to users desktop computers, is essential. There are many threats to users computers, ranging from remotely launched network attack to malware and viruses that are spread through e-mails,...
eROR: Register of Ordinary Residents for the Management of Citizen Database
Ordinary Resident Register (ORR) is a physical register maintained in the state of Tripura, at the lowest tier of local self-government (urban as well as rural), to record the details of the citizens. Citizens are not entitled to civic services and benefits, unless their names are recorded...
Publishing of Exam Results & Online Counselling from NIC Data Centre T
NIC Data Centre, Delhi has always played a proactive and pivotal role in providing robust, reliable and secure service-delivery platform to its hosted applications, be it a website, portal or any e-Governance project. Continuing with its decade long success trail, this year too, NIC Data Centre...
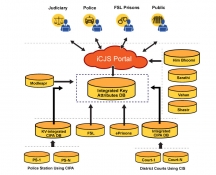
iCJS: Inter-operable Criminal Justice System
The Interoperable Criminal Justice System (iCJS) has been developed for the process of speedy justice by facilitating data-exchange between the courts, police/prosecution, jails and the forensic labs. The application has been developed by NIC for the District courts, prisons and Police...
CollabDDS: Network Enabled Medical Diagnosis and Education in Skeletal Imaging using X-Rays Dr. O. P. KHARBANDA
National Knowledge Network (NKN) due to high bandwidth and low latency has ensured the creation of applications which will be beneficial to all stakeholders in science, technology, governance and research & development. A model project funded by NKN and executed by NIC, New Delhi; AIIMS...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


