Articles
MUZAFFARNAGAR: Treading fast on e-Governance turf
Muzaffarnagar, located in the northern part of Uttar Pradesh is popularly known as The Sugar Bowl of India. With a population of 41,38,605 (Provisional figures of the 2011 census of undivided Muzaffarnagar) the district spreads over an area of 4049 square kilometers and has 4 tehsils, 9 development...
HAMIRPUR: Bridging the Digital Divide
Hamirpur, one of the twelve districts of beautiful state of Himachal Pradesh, lies in the middle of the Shivalik Ranges. It is the states most literate district and well connected by roads. Majority of the people serve for defense forces thus popularly known as Veer Bhoomi. The district is...
BHILWARA: From Textiles to Excellence in ICT
Bhilwara has earned a prominent spot on the industrial map of India. It has emerged as Indias largest manufacturer of fabrics. Also known as textile city of India, it is a famous industrial town in Rajasthan with presence of renowned industrial groups. The fabric is exported to countries like...
RESPONSIVE WEB DESIGN: Device Friendly Web Viewing
India is a fast growing market for internet users. Technological innovations and availability of new handy devices help people to access internet more on their smart phones, tablets, net-books and other such mobile devices than the desktop PCs. Nowadays, every website owner wants a mobile version...
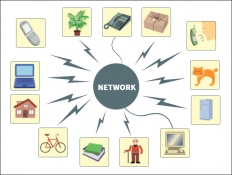
UBIQUITOUS PROMISES: Internet of Things
Human civilization over time devised various ways to communicate and interact with one another through the means of postal/telephonic/Internet based communication. Present world is enjoying all time connected phenomena, riding on the successful implementation of Internet and Internet based technology....




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


