Articles
LINKED DATA: Road to Intelligent Web
Linked data is emerging as a new paradigm for publishing and interlinking data from different data sources and evolving web from Web of linked documents into the Web of linked data. The global database created by linked data provides flexible interorganizational collaboration and dynamic...
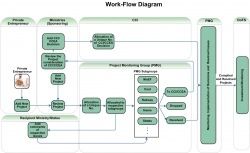
e-CCI: PROJECTS MANAGEMENT SYSTEM
With an objective to create an institutional mechanism for tracking the stalled investment projects, both in the public and private sectors, and to eradicate the implementation bottlenecks so faced on a fast track basis, a Cabinet Committee on Investment (CCI) Cell has been constituted in the Cabinet...
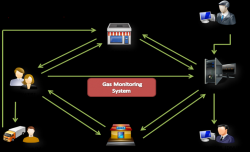
EASYGAS, KISAN: Citizen-Centric IT Innovations from Gonda, Uttar Pradesh
Achieving milestone is not an everyday business. Claiming appreciation for achievement is even tougher. The feeling goes beyond the expected elation, when endeavour, designed and perspired for common good catches peoples eyes to attain recognition. Project EASYGAS and project KISAN, the two...
LEVERAGING INTEGRATED NPR & SECC-2011 FOR ESTABLISHING NFSA 2013 DATABASE & SRDB IN HARYANA
On July 9, 2013, Government of Haryana announced implementation of National Food Security Act 2013 (NFSA 2013) from 20 August 2013 and decided to utilize provisional data of Socio Economic and Caste Survey (SECC-2011) and National Population Register (NPR-2011) on as-is-where-is basis for identification...
ICT ENABLED IMPLEMENTATION OF FOREST RIGHTS ACT 2006 IN MAHARASHTRA
Today, Information and Communication Technology has infiltrated the remotest corners of the Earth. The Government of Maharashtra came up with an ICT based innovation to preserve the forests and the rights of those who live in these remote forest areas. Implementation of GIS and other ICT...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


