Articles
CSI-NIHILENT E-GOVERNANCE AWARDS 2012-13
.CSI Nihilent e-Governance Awards have been instituted to acknowledge the exemplary initiatives/projects/services in the realm of e-Governance. Running into its second decade, the award is a golden yardstick for evaluating the mileage of various e-Governance initiatives running in the country. Alike previous...
MALKANGIRI: e-Governance in the land of Primitive Tribes
Malkangiri district came into existence after the reorganization of Odisha state on 2nd October 1992. Covering an area of 5,791 sq. kms, almost the whole of district is covered with vast dense jungles, with tribal population comprising of primitive tribes notable among them are Bondas, Koyas,...
JIND: Providing Innovative Technology Solutions for People
The district Jind derives its name from Jaintapuri, a town that grew around the temple of Jainti Devi (the goddess of victory) where Pandavas offered prayers for their success in their battle against Kauravas. It is one of the oldest districts of Haryana, comprising of 3 sub-dvisions, 4 tehsils,...
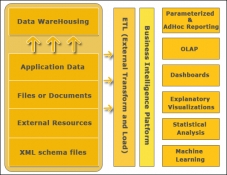
BIG DATA ANALYTICS
and the endless possibilities that it promises in all spheres of life has led to the coining of the term Big Data. Gartner defines Big Data as high volume, velocity and variety information assets that demand cost-effective, innovative forms of information processing for enhanced insight and decision making....
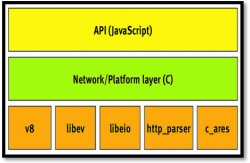
NODE.JS: Lightweight, Event driven I/O web development
As number of internet users is rising steadily, the servers are getting flooded with their requests and responses. To advert this situation, the servers are highly equipped with the high-end hardware like maximum number of core/processor, memory, enhanced I/O devices etc. But, these arrangements...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


