Articles
PAKUR: Empowering Citizens through e-Governance
Situated in the north-eastern corner, Pakur is one of the twenty four districts of the Jharkhand state and is topographically divided into three distinct regions - hilly, rolling and alluvial. The district is predominantly agricultural based and the main occupation of the people is cultivation....
SIRSA: Revolutionizing Governance Through ICT
Sirsa is said to be one of the oldest places of Northern India and its ancient name was Sairishaka, which finds its mention in Mahabharata, Panini's Ashatadhayayi and Divyavadan. It must have been a flourishing city in the 5th century B.C. as mentioned by Panini. Sirsa forms the extreme...
Achieving High Availability of Databases through Failover Clustering for databases using Microsoft SQL Server 2008
One of the major challenges which IT systems face today is System Availability. Availability is critical in terms of components viz., Web Server, Database Server, and Network. Without availability, services fail, SLAs exceed, revenue is lost and finally a bad publicity can leave a lasting effect...
Leveraging Emerging Technologies in Integrated Property Registration & Land Records SolutionIICT
Use of technology in registration of land records
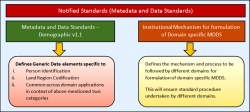
Role of Metadata and Data Standards in e-Governance
Seamless sharing and integration of data among various applications within and across the domains in e- Governance system augments its efficacy. In our country, a large number of the e- Governance applications developed within various domains are still being used in silos as they failed to...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


