Articles
e I T I s : Standardizing Industrial Training Institutes in Punjab
Due to ever increasing demand for skilled manpower, large scale establishment of the Industrial Training Institutes (ITIs) is taking place both in public as well as in private sectors. At the same time, there is a need to regularly monitor the infrastructure, results, faculty, trainees etc. of...
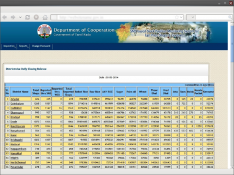
SMS BASED MONITORING SYSTEM FOR FAIR PRICE SHOPS IN TAMIL NADU
The Co-operation, Food and Consumer Protection Department of the Government of Tamil Nadu has the operational responsibility of identification of beneficiaries, issuance of ration cards and supervision of movement and distribution of food grains from godowns through Fair Price Shops located all...
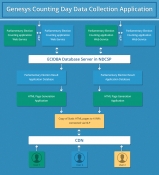
Collection, Consolidation and Dissemination of Results of General Elections 2014 using ICT Tools
India is the largest democracy of the world. Considering vast geographical expanse and large size of electorate, carrying out free and fair election process in India is quite complex and challenging. With 814.5 million registered voters taking part, General Elections 2014 have proved to be biggest...
SHIMLA: Bringing ICT at the doorsteps of the Citizens
Shimla, popularly known as the Queen of Hills, is the capital of Himachal Pradesh. It is famous worldwide as a popular tourist destination. Shimla has witnessed many historical events during British rule and in postindependence period. The town of Shimla is built over several hills and connecting ridges....
KANNUR: ICT for the Land of Looms and Lore
It is assumed that the name Kannur has derived from one of the deities of the Hindu pantheon Kannan (Lord Krishna) and Ur (place) making it the place of Lord Krishna. The district is known as the Land of Looms and Lore. Earlier the district was named Cannanore which is anglicised from of Kannur. The...




 Subscribe
Subscribe


 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


