Articles
ONLINE DRUG INVENTORY & SUPPLY CHAIN MANAGEMENT SYSTEM OF HARYANA
With the aim to provide Right Quantity of Right Product on Right Place on Right Time in Right Condition at Right Cost for Right People and also to streamline the distribution of drugs to institutions and ensure availability of drugs at all times, a new, innovative system called online Drug Inventory...
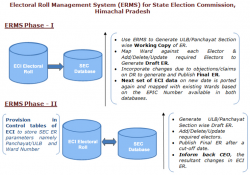
ELECTORAL ROLL MANAGEMENT SYSTEM (ERMS) FOR STATE ELECTION COMMISSION, HIMACHAL PRADESH
Electoral Roll Management System (ERMS) aims to leverage the use of voters data/electoral rolls generated by Election Commission of India (ECI) during Parliament and State Assembly elections for the purpose of Panchayat/ Urban Local Bodies elections, thus thwarting the duplicacy in...
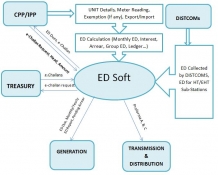
EDSoft: Online Collection and Monitoring of Electricity Duty in Odisha
The EDSoft system radically enhances collection of electricity duty in the state of Odisha. The system builds consumer database, calculates Electricity Duty, facilitates e-payment, monitors arrear, exemption, export grants etc. ensuring transparency at all levels.
Launch of Prime Minister's Website
Just seconds after Shri Narendra Modi was sworn-in as the 15th Prime Minister of India, the official website of the Prime Minister of India http:// pmindia.nic.in/ was made live by NICs web development team with active support from NIC Cell at Prime Minister Office (PMO). Brimming with latest...
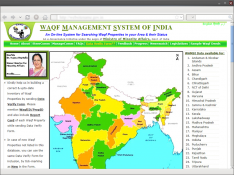
Waqf Management System of India (WAMSI)
Waqf is the permanent dedication by a person professing Islam, of movable or immovable properties for any purpose recognized by the Islamic law as pious, religious or charitable. Waqf Management System of India (WAMSI) is an integrated on-line work flow based Information System for the management...




 Subscribe
Subscribe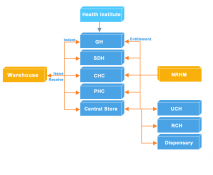

 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


