News
eGov workshop at Azamgarh, Uttar Pradesh
Training was imparted on State Portal, SSDG and e Forms to the government officials and employees of various departments in the district by Shri G. P. Singh District Informatics Officer (DIO) NIC,in the presence of DM Azamgarh Shri Pranjal Yadav, on 10th July 2012. Officials from all the line departments...
eGovernance workshop at Fatehpur, Uttar Pradesh
The State Portal, SSDG and eForms projects will be operational in the state from 1st August 2012. The project is aimed to provide relief to the rural masses from the unnecessary harassment, faced at time of vailing government services. A training program for district administration officials was organized...
eGovernance workshop at Mahamaya Nagar (Hathras), Uttar Pradesh
The national eGovernance programme to provide quick and cost effective services to the citizens was initiated in Mahamaya Nagar (Hathras) in Uttar Pradesh on 13th July 2012. The first step was to impart training to the government officials on the services to be offered through the new system and the...
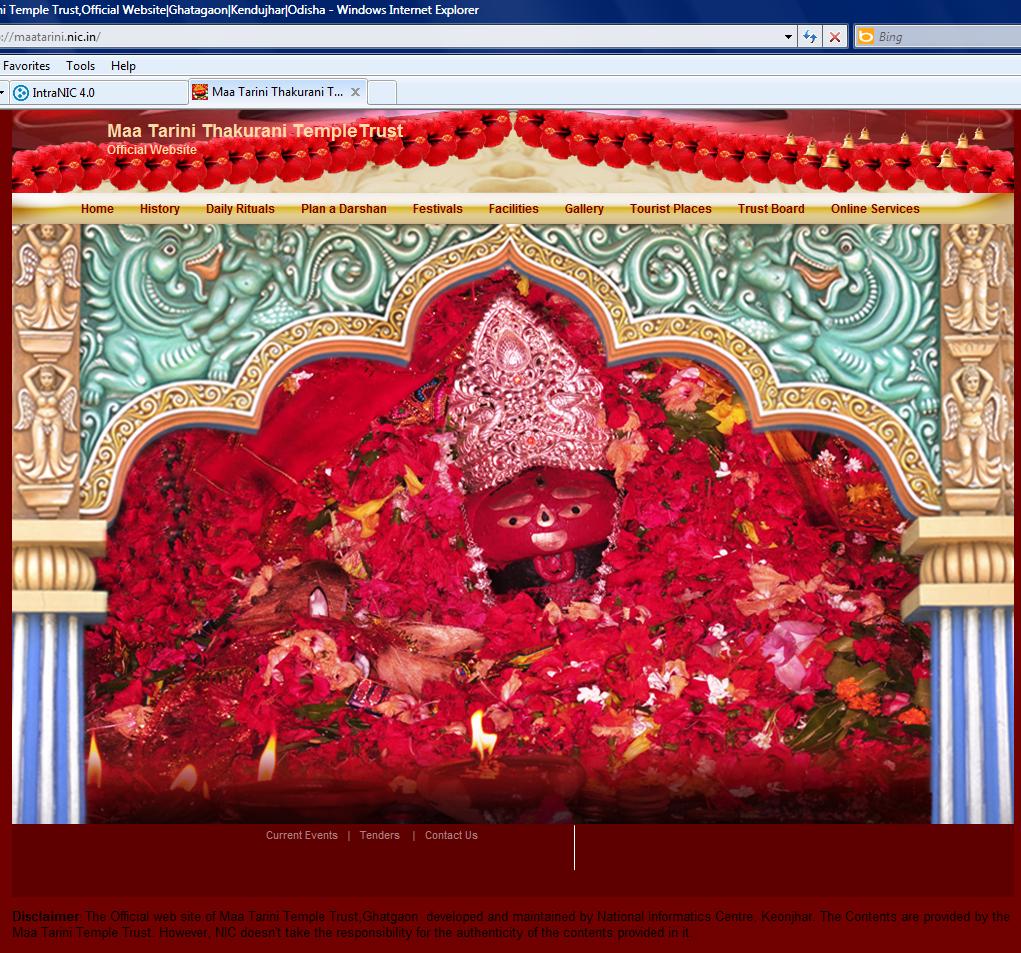
Website of Maa Tarini Temple Trust, Ghatagaon, Keonjhar, Odisha launched
The newly developed website of Maa Tarini Temple Trust, Ghatagaon, Keonjhar, Odisha (maatarini.nic.in) was launched by Shri D. V. Swamy, IAS, Collector and District Magistrate, Keonjhar on dt-10.07.2012 in the Kalyanmandap Hall of Temple Trust, Ghatagaon. Addressing on the occasion Shri...
eGovernance workshop in Aligarh, Uttar Pradesh
A workshop was held at Aligarh on 10th July 2012 which emphasized on the benefits of eGovernance services for the citizens. Shri Alok Kumar, District Magistrate, Aligarh, along with around 50 senior officials of the district administration including ADM, CDO, SDMs, DSWO, DSO etc. participated in the...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


