News
State level Knowledge Sharing workshop For DIO/ ADIOs, NIC, Odisha during 10th -11th January 2019
The state level DIOs meet was organized at NIC State Center, Bhubaneswar, Odisha, during 10th and 11th January 2019 in presence of Smt. Nandita Choudhury, DDG & State Coordinator, Odisha. The inaugural session was chaired by Smt. Pratibha Singh, DDG & SIO. Shri C. J. Venugopal, IAS , Principal...
J and K - e-Challan System inaugurated by Commssioner Transport
Commissioner Transport, J&K Dr. S. P. Vaid inaugurated e-Challan Project today on 04.01.2019 which will help in improving service access and transparency in the system. Dr. Vaid said e-Challan mobile app is integrated system linked with Vahan and Sarathi applications which cover all...
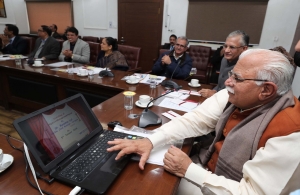
Honourable Chief Minister Sh. Manohar Lal Khattar launched Litigation Management System (LMS) on 5th Jan 2019
At the launch event of Litigation Management System (LMS) on 5th Jan 2019, Hon’ble Chief Minister Sh. Manohar Lal Khattar was present along with Advocate General Haryana Sh. Baldev Raj Mahajan, Chief Secretary, Haryana Sh. D.S.Dhesi and some other senior Officials....
Haryana:- Launch of Antyodaya Saral Project by Honourable Chief Minister Haryana on Good Governance Day
On good governance day i.e. 25th December 2018, Hon’ble Chief Minister Haryana Sh. Manohar Lal inaugurated series of events at Mini Secretariat Karnal for ‘Antyodaya Saral’ project, in the presence of Principal Secretary E&IT, Principal Secretary Social Justice & Empowerment...
Chief Secretary, Himachal Pradesh Launches Traffic Management Mobile App
Sh. B.K. Agarwal, Chief Secretary, Himachal Pradesh launched the Traffic Management mobile App on 22nd December 2018 at Shimla. Sh. Manoj Kumar, ACS Home, Health, Sh. R.D. Dhiman, ACS Forest, Personnel, Sh. Probodh Saxena, Principal Secretary, Power, UD, TCP, Sh. Onkar Chand Sharma, Principal Secretary,...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


