Honourable Chief Minister Sh. Manohar Lal Khattar launched Litigation Management System (LMS) on 5th Jan 2019
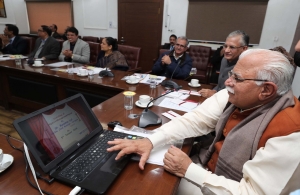

At the launch event of Litigation Management System (LMS) on 5th Jan 2019, Hon’ble Chief Minister Sh. Manohar Lal Khattar was present along with Advocate General Haryana Sh. Baldev Raj Mahajan, Chief Secretary, Haryana Sh. D.S.Dhesi and some other senior Officials. SIO Haryana briefed the Objectives and benefits of Litigation Management System at the launch event. From NIC, this project is leaded by State Informatics Officer Sh. Deepak Bansal and developed by Amit Kumar Scientist-B, NIC Haryana.
The Litigation Management System (LMS) is designed for departments, corporations, boards and other state bodies to monitor the status of the case related to them. This PHP and Postgresql based application is developed by NIC Haryana.
LMS is a Generic, integrated workflow based system to be implemented across Haryana Govt. The User Departments of LMS will enter their cases in the system. This software will be integrated with High Court for fetching out the data for cases related to the different departments. The Office of Advocate General, Haryana will work as a State Nodal Office. The system shall be web based and accessible over the internet. There will multiple levels of users who can access the system as per the limitation of the scope of work.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


