e-Municipalties
Karnataka: Empowering Rural Citizens by Taking ICT to Their Doorsteps
Bridging the gap between the haves and the havenots has been the focus of the Government of Karnataka. The aspiration is being fulfilled by continuously providing more and better services to the citizens. The rural citizens are empowered by taking ICT to their doorsteps thus enabling them...
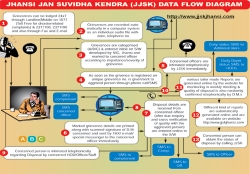
Jhansi: Leading From the Front
'Leading from the front' is synonymous with Jhansi, be it the First Freedom Struggle of India or the modern day ICT based Governance, Jhansi has been the torch bearer with earnest dedication. Centuries have moved from twentieth to twenty first but the will to provide good governance...
Muzaffarpur: A Major Hub for e-Governance in North Bihar
Muzaffarpur, a major town of north Bihar, situated on the Indo-Gangetic plain, has earned international encomiums for its delicious Shahi Litchi which are exported to other parts of the country and even abroad. Muzaffarpur has innumerable historical sites and monuments. There are a lot of Buddhist Viharas...
Jalgaon: Focusing on Citizen Centric e-Governance
Located in the north-west region of Maharashtra, Jalgaon is famous across the world for its world famous tourist and heritage site Ajanta Caves which is about 50 kms from the district headquarters. Owing to its main crop of Banana the district is also known as Capital of Banana and has a population of...
e-District - Uttar Pradesh takes the Lead
Uttar Pradesh became the first state in the country to roll out e-District project in 6 pilot districts of the state. e-District is a State Mission Mode Project under the National e-Governance Plan (NeGP) of Ministry of Communications & IT. The project seeks to automate the complete workflow and...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


