Automation
Revenue Court- Case Monitoring System of Odisha
Petitioners can now register a case online and track its status. Cause list is generated dynamically, which is published on the portal after approval by the competent authority. Hearing Notice is served online to the petitioner/ advocate and opponents by way of SMS, e-mail and physically through the...
HOT DAK Tracking System
HOT DAK Tracking System was conceived and developed for online tracking of important and High Priority References across the Offices to monitor and achieve timely disbursal of References.
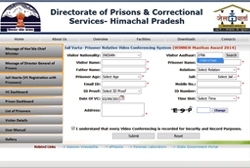
JailVaarta: Innovative software to facilitate Video Conferencing of Prisoners with Relatives
JailVaarta is an innovative application developed by NIC, for primarily facilitating the prison inmates and their relatives to interact conveniently without the relatives visiting prison.
Joint Seat Allocation System
Joint seat allocation to government funded technical institutes based on three independent entrance examinations using multiple ranks is a watershed event in engineering admissions in India.
Aadhaar enabled PDS System (AePDS) - electronic Point of Sale (ePoS)
Andhra Pradesh is the first State in the country to implement ePoS in 100�ir price shops with the integration of FCI & MLS points (Supply Chain Management System) for lifting of Stock and ration portability. The system enables monitoring the Sales & Stock availability at every FPS. All PoS devices...




 Subscribe
Subscribe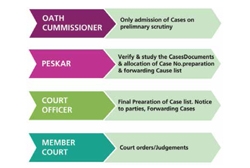




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


