Automation
Aadhaar Authentication Platform
The Authentication Services is integrated with 110 plus applications of States & Central Government Departments and Ministry with the monthly transaction of around 12 Crores in the month of November 2017. Indian Army, Public Distribution System, Digital Locker, CBSE, Jeevan Pramaan, Biometric...
Lsyncd (LIVE SYNCING DAEMON)
Lsyncd is a light-weight data replication tool which is free, easy to install and convenient to configure. It is an open source technology based, ultimate host to host replication or mirroring tool with very minimal configuration, cost effective and can assure the RPO in minutes or even seconds.
Appscape
Mobile Apps today have become the inevitable component of any online application. Apps increase the popularity of an application by providing anytime anywhere access. In the era of Digital India, mobile Apps are considered as a basic necessity, and no longer a luxury.
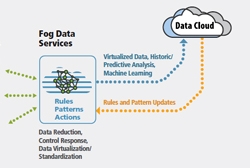
FOG Computing
Fog computing was introduced to meet objectives like improving efficiency and trim the amount of data to be transmitted for processing, analysis and storage, place the data close to the end user and finally provide security and compliance to the data transmission over cloud. Cloud is located up in the...
eAwas Software & App of Chandigarh
eAwas, which aims at bringing transparency and enabling hassle free allotment of Government Houses, is a step towards taking Chandigarh into the Digital Age and using technology to solve real world problems. The portal (http://eawas.chd.gov.in) enables online submission of applications by employees and...




 Subscribe
Subscribe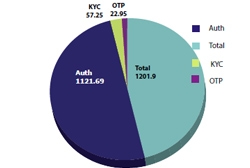




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


