Technology
WEB ANALYTICS SERVICE: RANKING GOVERNMENT WEBSITES
Web Analytics Service, an initiative under the National Portal of India, is offered by NIC for the Indian Government Websites. Web traffic to Government Websites is tracked and analyzed by NIC to help them understand the usage of their website & enhance its reach. Rank of websites is calculated based...
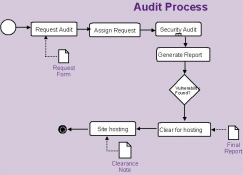
AUDIT STATUS MONITORING SYSTEM- A SYSTEM FOR FACILITATING WEB APPLICATION SECURITY AUDIT SERVICES
Strengthening and enhancing the security posture of systems and services is one of the objectives of any organization dealing with information assets of different organizations and departments of Government of India. The Cyber Security Division of NIC is dedicated to this task, having adopted a multi-pronged...
DISSECTING A MALWARE ATTACK
A malware can sneak into a system in the guise of a mail attachment or the system can get infected by simply visiting a malicious website. User is often taken off-guard while the malware sneaks into the system and compromises its integrity.
NoSQL- NO PROBLEM WITH 'BIG DATA'
Tabular data remains tabular and the spreadsheet is still a business's favourite data modeling tool. SQL is not going away anytime soon. However until now we've been creative in working with and around the constraints of a typical relational datastore. NoSQL offers the chance to think differently...
e-Office: COLLABORATION AND MESSAGING SERVICE
eOffice-CAMS is focused on providing effective communication between departmental applications through collaboration and the obvious solution is to have Collaborative service. The idea is to facilitate action oriented team to work together over a geographical distance and let internal users, systems...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


