Technology
NATIONAL PORTAL OF INDIA 2.0: A Gateway to Government Information and Services
The India Portal (india.gov.in) is a Mission Mode Project under integrated services category of the National e-Governance Projects (NeGP) to bring in a Single-Windowaccess to Government information and services.
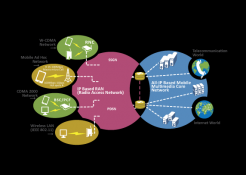
LONG TERM EVOLUTION(4G) - A Generation Gallop Technology
Earlier, downloading a large file used to take 30 minutes to a couple of hours depending on the broadband speed. Now the same task is possible in few minutes time even while on travel! The LTE (Long Term Evolution or 4G) has made this possible with its lightning fast Internet capabilities.
MedLEaPRFIRST STEP TOWARDS ICT ENABLED INTEGRATED JUSTICE DELIVERY SYSTEM
Medico Legal Examination and Postmortem Reports System (MedLEaPR) is a generic software developed by NICHaryana to facilitate computerization of MLRs & PMRs. Further, the system is workflow based, which provides requisite access security, based on roles & responsibilities...
e-OFFICE: DIGITAL SIGNING TOOL FOR SECURE DOCUMENTS
Automation has become an integral part any organization through information digitalization leaving away the manual process using physical paper documents. Instead of routing the paper documents manually, the electronic channels have been used extensively for transitioning the documents in digital form....
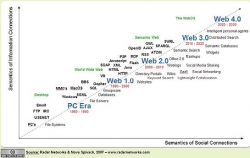
INTERNETING IN THE FUTURE - WEB 3.0
Internet started as a military exercise to link offices across the USA, has become ubiquitous in every sphere of human lives whether living in rural, urban or semi-urban habitats. The information flow from top to bottom and vice-versa has made the people more knowledgeable not only about their rights...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


